Exploració per tema "Classificació INSPEC::Cybernetics"
Ara es mostren els items 1-13 de 13
-
A personal account of Turing’s imprint on the development of computer science

(Elsevier, 2012)
(Elsevier, 2012)
Article
Accés obertThe rst part of the XX century saw the development of the digital computer and the eld of computer science. In the present paper, we sketch our vision of that period and of the role that Alan Turing and some of his ... -
A virtual actuator approach for the secure control of networked LPV systems under pulse-width modulated DoS attacks

(2019-01-01)
(2019-01-01)
Article
Accés obertIn this paper, we formulate and analyze the problem of secure control in the context of networked linear parameter varying (LPV) systems. We consider an energy-constrained, pulse-width modulated (PWM) jammer, which corrupts ... -
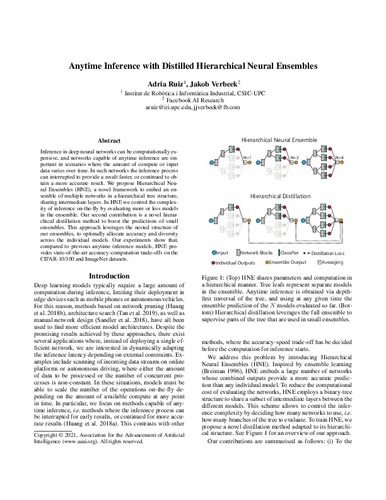
Anytime inference with distilled hierarchical neural ensembles

(2021)
(2021)
Text en actes de congrés
Accés obertInference in deep neural networks can be computationally expensive, and networks capable of anytime inference are important in mscenarios where the amount of compute or quantity of input data varies over time. In such ... -
Computation of independent contact regions for grasping 3-D objects

(Institute of Electrical and Electronics Engineers (IEEE), 2009-08)
(Institute of Electrical and Electronics Engineers (IEEE), 2009-08)
Article
Accés obertPrecision grasp synthesis has received a lot of attention in past few last years. However, real mechanical hands can hardly assure that the fingers will precisely touch the object at the computed contact points. The concept ... -
DAE Methods in Constrained Robotic System Simulation:

(Centro de Investigación en Computación, 1998-03)
(Centro de Investigación en Computación, 1998-03)
Article
Accés obertIn this paper a DAE formulation is used to model the behaviour of constrained robotic systems. This formulation allows to specify in an easy and clear way the constrained behaviour of a robotic system. In order to better ... -
Detection of replay attacks in CPSs using observer-based signature compensation

(Institute of Electrical and Electronics Engineers (IEEE), 2019)
(Institute of Electrical and Electronics Engineers (IEEE), 2019)
Text en actes de congrés
Accés obertThis paper presents a replay attack detection method that addresses the performance loss of watermarking-based approaches. The proposed method injects a sinusoidal signal that affects a subset, chosen at random, of the ... -
Detection of replay attacks in cyber-physical systems using a frequency-based signature

(2019-03-01)
(2019-03-01)
Article
Accés obertThis paper proposes a frequency-based approach for the detection of replay attacks affecting cyber-physical systems (CPS). In particular, the method employs a sinusoidal signal with a time-varying frequency (authentication ... -
Dynamic equations of motion for a 3-bar tensegrity based mobile robot

(IEEE, 2007)
(IEEE, 2007)
Text en actes de congrés
Accés obertTensegrity structures can give a new approach to the construction of mobile robots with different shapes and properties that usual robots, wheeled or legged, do not have. Tensegrity are light, deformable structures that ... -
Generating predicate suggestions based on the space of plans: an example of planning with preferences

(2023-05-31)
(2023-05-31)
Article
Accés obertTask planning in human–robot environments tends to be particularly complex as it involves additional uncertainty introduced by the human user. Several plans, entailing few or various differences, can be obtained to solve ... -
Onto computing the uncertainty for the odometry pose estimate of a mobile robot

(IEEE, 2007)
(IEEE, 2007)
Text en actes de congrés
Accés obertSolving the navigation issue for a mobile robot in a 2D space requires using internal and external sensors, so researchers try to fuse data from different sensors using methods as for example Kalman filtering. Those methods ... -
Reachability and stabilization of scheduled steady-states for LPV single-input systems

(2019-05-01)
(2019-05-01)
Article
Accés obertThe aim of this work is characterizing the class of LPV systems that admit steady-state trajectories depending exclusively on the scheduling parameter. In particular, it will be shown that only certain parameter dependent ... -
Smartphone picture organization: a hierarchical approach

(2019-10-01)
(2019-10-01)
Article
Accés obertWe live in a society where the large majority of the population has a camera-equipped smartphone. In addition, hard drives and cloud storage are getting cheaper and cheaper, leading to a tremendous growth in stored personal ... -
Tensegrity frameworks: static analysis review

(Elsevier, 2008)
(Elsevier, 2008)
Article
Accés obertThis paper hands in a review of the basic issues about the statics of tensegrity structures. Definitions and notation for the most important concepts, borrowed from the vast existing literature, are summarized. All of these ...